Solana’s development team Anza announced on May 13, 2026 that Alpenglow, the network’s most ambitious consensus architecture overhaul to date, is now running on a community test cluster. The move puts validator operators in position to stress-test software that would fundamentally change how Solana reaches agreement on the state of its blockchain.
“Alpenglow is live on the community test cluster,” Anza wrote on X. “The biggest consensus change in Solana’s history, now running on validator infrastructure ahead of mainnet.”
The timing is notable. Solana has spent the better part of three years fighting a reputation for network instability during demand spikes, even as it simultaneously built one of the most active developer ecosystems outside Ethereum. Alpenglow represents an attempt to solve the first problem without sacrificing the throughput that made the second possible.
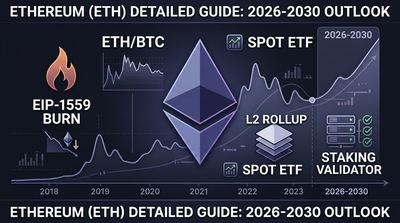
Proof-of-History Gets a Rethink
To understand what Alpenglow changes, you have to understand what Solana currently runs. The network uses a tripartite consensus approach: Proof-of-Stake for validator economics, Proof-of-History for transaction timestamping, and TowerBFT for the voting mechanism validators use to agree on blockchain state.
Proof-of-History deserves a moment of explanation because it is genuinely unusual. Most blockchains establish ordering by having validators agree on which transactions came first, a process that requires communication rounds and adds latency. Solana’s Proof-of-History instead uses a cryptographic clock. Each validator can independently verify the passage of time by computing a verifiable delay function, which produces a sequence of hashes that proves a specific amount of real time elapsed. Transactions get timestamped against this clock, reducing the coordination overhead needed for ordering.
The design worked well enough to give Solana sub-second block times and transaction costs measured in fractions of a cent. It also produced outages. During periods of extreme demand (NFT mints, memecoin frenzies, liquidation cascades), the network has historically struggled. Transactions would fail, the network would stall, validators would fall out of consensus. The community has grown accustomed to periodic post-mortems.
Alpenglow targets this pain point by rearchitecting the finality process itself. While Anza has not published exhaustive technical documentation for the test cluster release, the stated goal is to dramatically reduce finality times and improve network responsiveness, particularly under load.
For context on what Solana is trying to protect: the network processed a daily average of over 65 million transactions in Q1 2026, according to Solana Foundation data. Its fear and greed readings have tracked closely with retail participation in memecoins and DeFi protocols built on the chain. A consensus upgrade that degrades throughput or increases costs would threaten that activity.
The tension between security upgrades and performance is not theoretical for Solana. As we reported in April, Solana faces a brutal choice between quantum security and blazing speed, with quantum-resistant cryptography potentially slashing transaction speeds by 40%. Alpenglow represents a different trade-off calculation: rather than adding security features that slow the network down, the upgrade attempts to make the existing security model execute faster.
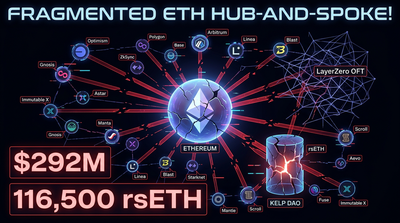
LayerZero’s Belated Mea Culpa
While Solana prepares for its consensus transition, the cross-chain infrastructure space is still cleaning up from April’s $292 million Kelp DAO exploit. And LayerZero, after weeks of pointing fingers at the application layer, finally acknowledged its own role.
“First things first: an overdue apology,” LayerZero wrote in a blog post. “We made a mistake by allowing our DVN to act as a 1/1 DVN for high-value transactions. We didn’t police what our DVN was securing, which created a risk we simply didn’t see. We own that.”
The admission represents a significant reversal. When the hack first came to light, LayerZero’s public position was that Kelp DAO had chosen a risky configuration: a “1-of-1” setup in which only a single decentralized verifier network (DVN) needed to approve cross-chain transfers. This created, in effect, a single point of failure that North Korean attackers exploited.
A DVN is infrastructure that verifies whether a transaction moving assets between blockchains is legitimate. Think of it as a notary for cross-chain activity. In a multi-DVN configuration, multiple independent verifiers must agree that a transfer is valid before it executes. In a 1-of-1 configuration, you are trusting one verifier entirely.
LayerZero’s initial framing put the blame squarely on Kelp for selecting this configuration. The new admission shifts responsibility: LayerZero’s own verification infrastructure was available for this configuration, and the protocol failed to prevent high-value assets from being secured by a single point of failure.
The $292 million figure makes this the second-largest DeFi bridge exploit in history, trailing only Ronin’s infamous 2022 breach. The attribution to North Korean attackers follows a pattern. State-sponsored hackers from the DPRK have been linked to multiple major crypto thefts, including the Ronin hack, with stolen funds reportedly used to finance weapons programs.
For protocols evaluating cross-chain infrastructure, LayerZero’s admission raises uncomfortable questions. The company’s value proposition centers on omnichain interoperability, the ability to move assets and messages across dozens of blockchains through a single unified framework. That pitch only works if the verification layer is trustworthy. Allowing a 1-of-1 configuration to secure hundreds of millions of dollars suggests either a gap in risk assessment or a willingness to prioritize adoption over security.
LayerZero’s blog post did not detail what safeguards would prevent similar configurations in the future, though the company indicated it would implement changes. For now, the damage extends beyond the stolen funds. The reputational hit affects the entire cross-chain bridging sector, which has been responsible for some of the industry’s most spectacular losses. Bridges are high-value targets precisely because they hold large pools of assets and create trust assumptions that attackers can exploit.
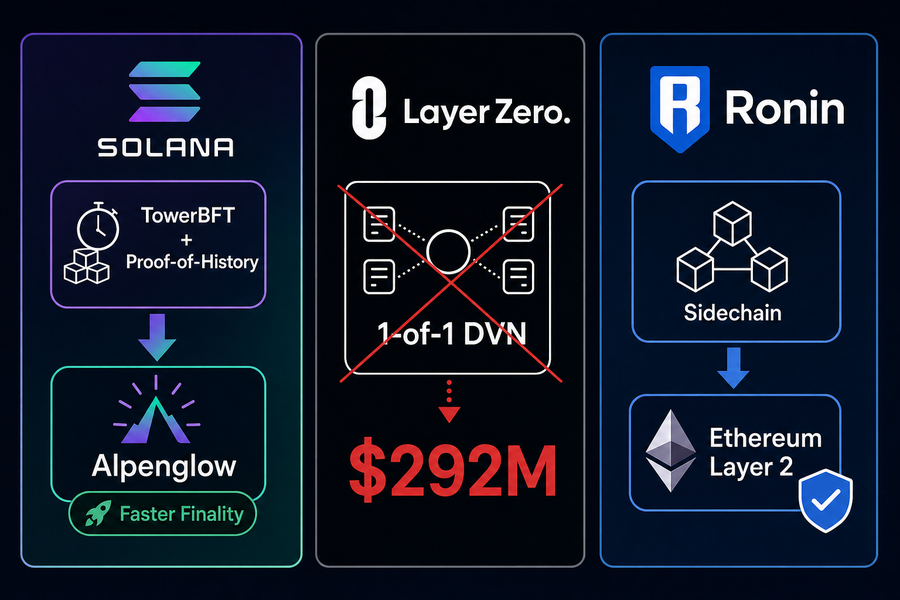
Ronin Returns to the Mothership
Speaking of bridge exploits: Ronin, the gaming-focused blockchain that lost $625 million in 2022 in what remains the largest DeFi bridge exploit ever, is changing its security model entirely.
On May 12, 2026, Ronin executed a hard fork at block 55,577,490, transitioning from an independent sidechain to an Ethereum layer 2. The network indicated the migration would result in approximately 10 hours of downtime for users.
“Four years ago, we launched Ronin because Axie Infinity needed a faster and more efficient network,” the project said when announcing the migration in April. “It worked. Axie Infinity onboarded millions of gamers to crypto, and Pixels proved that it was possible to do it again.” The time had come, they added, to plug “back into the mothership.”
The architectural difference between a sidechain and a layer 2 matters for security. A sidechain runs its own consensus mechanism and security model, connected to the main chain (in this case, Ethereum) through a bridge. A layer 2 derives its security from the underlying blockchain, posting transaction data or proofs to the main chain in a way that inherits Ethereum’s security guarantees.
Ronin’s 2022 hack exploited precisely this distinction. Attackers compromised validator keys on the sidechain’s bridge, allowing them to forge withdrawals. Because the sidechain’s security was independent of Ethereum, the only protection was the validator set itself. Once attackers controlled enough validators, they could drain the bridge.
As an Ethereum layer 2, Ronin’s security model changes fundamentally. Transaction finality ties back to Ethereum’s consensus. Bridge operations can use Ethereum’s rollup proofs rather than relying solely on a separate validator set. The attack surface shrinks.
For the gaming use case Ronin targets, this creates a trade-off. Layer 2s must post data to Ethereum, which introduces costs and latency that pure sidechains avoid. Ronin’s bet is that the security improvement is worth that friction, particularly given how catastrophically the sidechain model failed in 2022.
The transition also reflects broader industry learning. In 2022, sidechains were a common scaling approach. Today, the market has largely moved toward rollup-based layer 2s (optimistic rollups and zk-rollups) that maintain tighter security links to underlying chains. Ronin’s migration is late by industry standards, but it finally aligns the network with current best practices.
Clear Signing Takes Aim at Phishing
The final development in this week’s protocol roundup targets a different kind of vulnerability: the human kind.
The Ethereum Foundation, alongside a group of major crypto wallet developers, unveiled a new standard called “Clear Signing.” The goal is to replace the confusing hexadecimal transaction data users currently see when approving Ethereum transactions with simple, human-readable explanations of what they are actually agreeing to.
If you have used a crypto wallet, you have encountered the problem Clear Signing addresses. You click “approve” on a transaction, and the wallet shows you something like a wall of hexadecimal code or an opaque function call. You probably have no idea what you are actually authorizing. You click confirm anyway because the alternative is not using the application.
This pattern has fueled countless phishing attacks. A user visits a malicious site that looks legitimate. The site requests a signature. The user sees gibberish, assumes it is normal, and approves. The signature turns out to authorize an unlimited token allowance, or a transfer to an attacker’s address, or a contract interaction that drains their wallet.
Clear Signing attempts to solve this by translating transaction data into plain language. Instead of seeing “0x095ea7b3000000000000000000000000…,” a user would see something like “Allow [contract name] to spend unlimited USDC from your wallet.” The difference between understanding and not understanding what you are signing is the difference between getting phished and not.
The standard is not just an interface improvement. It requires coordination across the wallet ecosystem to agree on how different transaction types should be described, what risk levels warrant warnings, and how to handle edge cases where transactions cannot be clearly described. The Ethereum Foundation’s involvement signals that this is intended as an ecosystem-wide standard rather than a proprietary feature.
For anyone tracking the broader security landscape, Clear Signing fits into a pattern. As the industry matures, the lowest-hanging fruit for attackers shifts. Smart contract vulnerabilities still exist, but major protocols have been audited repeatedly, and bug bounties create economic incentives to report rather than exploit. Social engineering and UI manipulation have become relatively more attractive attack vectors. Clear Signing addresses that shift.
The standard also connects to larger questions about self-custody. Critics of crypto have long argued that expecting average users to understand cryptographic signatures is unrealistic. Clear Signing is an acknowledgment that the critics had a point, while maintaining self-custody as the model. You do not need to understand the cryptography; you need to understand what action you are authorizing. Whether wallets implement Clear Signing consistently, and whether users actually read the explanations, will determine whether the standard achieves its goals.
What Connects These Four Stories
On the surface, Alpenglow, LayerZero’s apology, Ronin’s migration, and Clear Signing are four separate news items. But they share a theme: infrastructure maturation under pressure.
Solana’s consensus overhaul responds to years of criticism about reliability. LayerZero’s admission comes after a nine-figure loss forced accountability. Ronin’s layer-2 transition abandons an architecture that already failed catastrophically. Clear Signing addresses a vulnerability class that has drained millions from users who did nothing obviously wrong.
Each represents the industry learning from pain. The question, as always, is whether the learning sticks. Alpenglow will need to survive mainnet conditions before anyone can declare Solana’s stability problems solved. LayerZero’s promised safeguards are vague. Ronin’s layer-2 security benefits only matter if the implementation is sound. Clear Signing requires wallet adoption and user attention.
The derivatives and spot markets have largely priced crypto’s maturation as a given. Continued funding flows, ETF approvals, and institutional participation all assume the infrastructure will hold. Weeks like this one offer a reminder that holding is not automatic. It requires continuous effort to fix what is broken, often after something expensive breaks first.
Related Reading
- Browse coins by sector
- What is Ethereum? Smart contracts explained
- Technology news
- More on Solana
- More on LayerZero
References
- https://www.coindesk.com/tech/2026/05/13/the-protocol-solana-s-alpenglow-upgrade-is-live-for-testing
Note: nothing written here is a trade signal. Price movement discussed above is history, not a forecast. Verify anything you plan to act on.