CertiK researchers are warning cryptocurrency and fintech executives about a new malware campaign from North Korea’s Lazarus Group that transforms routine business communications into direct pathways for credential theft and data exfiltration. The operation, dubbed “Mach-O Man,” has already contributed to more than $500 million in losses from the Drift and KelpDAO exploits over the past two weeks.
The collective behind the campaign has accumulated an estimated $6.7 billion in stolen assets since 2017, cementing its position as one of the most persistent and well-funded cybercriminal operations targeting digital assets. What makes the current wave particularly concerning is the speed and sophistication of the attacks, which exploit social trust rather than technical vulnerabilities in blockchain protocols themselves.
“What makes Lazarus especially dangerous right now is their activity level,” Natalie Newson, a senior blockchain security researcher at CertiK, told CoinDesk on Wednesday. “KelpDAO, Drift, and now a new macOS malware kit, all within the same month. This isn’t random hacking; it’s a state-directed financial operation running at a scale and speed typical of institutions.”

How the ClickFix Social Engineering Attack Works
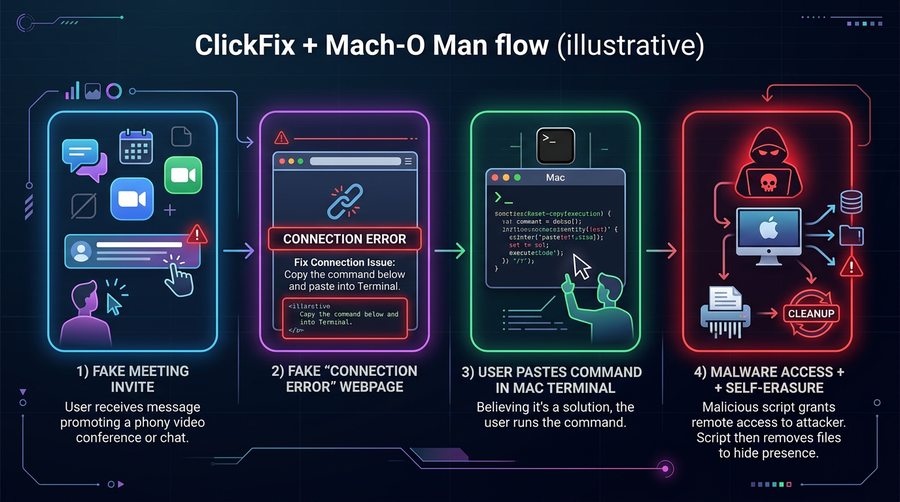
The Mach-O Man kit relies on a delivery method called ClickFix, a social engineering technique that manipulates victims into compromising their own systems. The attack begins with what appears to be an urgent meeting invitation sent via Telegram, directing targets to join a call on Zoom, Microsoft Teams, or Google Meet.
The link leads to a convincing but fake website that displays what looks like a connection error. The page then instructs the victim to copy and paste a simple command into their Mac’s terminal to “fix” the issue. By following these instructions, executives unknowingly grant attackers immediate access to corporate systems, SaaS platforms, and financial resources.
“The page looks real, the instructions seem normal, and the victim initiates the action themselves, which is why traditional security controls often miss it,” Newson explained. The self-initiated nature of the compromise makes it particularly insidious: endpoint protection software typically doesn’t flag commands that users deliberately execute.
Mauro Eldritch, a security expert and founder of threat intelligence firm BCA Ltd., described the attack’s effectiveness in targeting busy executives who might not think twice about troubleshooting a video call before an important meeting. The fake verification steps guide victims through keyboard shortcuts that run harmful commands, exploiting the trust people place in familiar corporate communication tools.
Security threat researcher Vladimir S. documented several variations of the attack on X, noting that Lazarus attackers have already hijacked decentralized finance project domains using the new malware. In these cases, legitimate websites were replaced with fake messages appearing to come from Cloudflare, asking users to enter commands to gain access.
North Korea’s Crypto Theft Machine Operates at Institutional Scale
The Lazarus Group’s recent $500 million haul from DeFi protocols underscores how North Korea has industrialized cryptocurrency theft as a national revenue source. The Drift and KelpDAO exploits weren’t isolated incidents but part of a sustained campaign that treats digital asset extraction as state business.
Newson urged the crypto industry to fundamentally shift how it perceives the threat. “The crypto industry needs to start viewing Lazarus the same way banks view nation-state cyber actors: as a constant and well-funded threat, not just another news headline,” she said.
The scale of operations has escalated dramatically. In previous years, major Lazarus-attributed hacks might occur quarterly or semi-annually. Now the group is executing multiple high-value operations within weeks of each other while simultaneously deploying new malware toolkits. This tempo suggests a significant expansion in operational capacity, likely supported by North Korean intelligence resources.
North Korea has turned crypto theft into what Newson described as “a lucrative national industry.” International sanctions have pushed the regime to develop alternative revenue streams, and cryptocurrency offers advantages traditional finance cannot: pseudonymous transactions, global reach without correspondent banking relationships, and assets that can be moved without physical borders.
The Arbitrum Security Council’s emergency freeze of $71 million from the Kelp DAO hackers demonstrated that the industry is developing countermeasures, but the recovery represented only about 25% of the stolen funds. The asymmetry remains stark: attackers need to succeed once, while defenders must prevent every attempt.
Why Mach-O Man Represents a New Threat Category for macOS
The “Mach-O” name references the native binary format used by Apple’s operating systems. Unlike cross-platform malware that relies on generic techniques, this kit is specifically tailored for the macOS environments where many crypto and fintech professionals operate. The sophistication suggests Lazarus has invested considerable resources in understanding Apple’s security model and developing exploits that work within it.
“It is a modular macOS malware kit created by Lazarus Group’s infamous Chollima division,” Newson said. “It uses native Mach-O binaries tailored for Apple environments where crypto and fintech operate.”
The Chollima division, named after a mythical Korean horse, has been linked to some of Lazarus Group’s most sophisticated operations. The unit’s focus on Apple systems reflects a strategic calculation: high-value targets in finance and technology disproportionately use Macs, and macOS has historically received less malware attention than Windows, potentially creating blind spots in security coverage.
What makes the kit particularly dangerous is its modular architecture. Rather than deploying a single monolithic payload, Mach-O Man can be configured with different components depending on the target environment. This flexibility allows attackers to customize their approach for specific organizations and evade signature-based detection that might catch more static malware.
Perhaps most concerning is the self-erasing capability. The malware deletes itself before victims realize they’ve been compromised, making forensic analysis extremely difficult. Security teams investigating a breach may find no traces of the initial infection vector, complicating both remediation and attribution.
“They likely don’t know it yet,” Newson said of many victims. “If they do, they probably can’t identify which variant affected them.”
The Spreading Threat Beyond Lazarus
While Lazarus Group created Mach-O Man, CertiK’s research indicates the kit has proliferated to other cybercriminal groups. This evolution from exclusive nation-state tool to broader criminal ecosystem mirrors patterns seen with other sophisticated malware that eventually leaked or was sold to third parties.
Newson emphasized the importance of distinguishing between the ClickFix delivery technique and the Mach-O Man payload itself. “It’s important to be clear because a lot of coverage is mixing up two separate things,” she noted. ClickFix is the social engineering method that tricks victims into executing commands, while Mach-O Man is the malware package that gets installed as a result. Understanding this distinction matters for developing effective defenses.
The commoditization of the attack kit means organizations face threats from multiple directions. State-sponsored actors like Lazarus bring resources and patience for high-value targets, but criminal groups using the same tools may cast wider nets, going after smaller crypto projects and individual holders.
For Bitcoin holders and traders using macOS systems, the threat landscape has materially shifted. Hardware wallets and air-gapped signing remain the gold standard for protecting significant holdings, but many operational tasks still require internet-connected devices. The attack surface extends beyond trading itself to any business communication that could serve as an entry point.
Ethereum DeFi participants face particular exposure given the ecosystem’s heavy reliance on web interfaces and browser-based wallet connections. A compromised system could allow attackers to manipulate transactions or drain connected wallets during routine protocol interactions. You can track developments across the broader DeFi ecosystem on our market overview page.
The attacks also highlight risks in the increasingly popular practice of holding operational meetings via video conferencing platforms. What once seemed like a security improvement over in-person meetings (no physical document exposure, recorded audit trails) now presents its own attack surface.
Defensive Measures and Industry Response
CertiK’s warning comes as the broader crypto security community grapples with an elevated threat environment. The confluence of Lazarus Group’s intensified operations, the specific targeting of macOS users, and the self-erasing nature of the malware creates a challenging defensive posture.
Traditional endpoint detection solutions may miss ClickFix attacks because the malicious commands are user-initiated. This shifts the defensive burden toward user education and process controls rather than purely technical countermeasures. Organizations should establish clear policies prohibiting the execution of terminal commands from external sources, regardless of how legitimate the request appears.
Verification procedures for meeting invitations become critical. Rather than clicking links in messages, executives should navigate directly to their organization’s calendar or meeting platform and verify any unexpected invitations through a separate communication channel. The minor inconvenience of double-checking pales against the potential for complete system compromise.
Network segmentation and least-privilege access controls can limit damage even when initial compromise occurs. If an executive’s workstation is breached, proper segmentation prevents lateral movement to critical infrastructure like hot wallet servers or trading systems. The principle of assuming breach, rather than attempting to prevent all intrusions, becomes increasingly relevant.
For organizations that handle significant crypto assets, air-gapped signing infrastructure for high-value transactions provides a backstop that software-based attacks cannot easily circumvent. Even if attackers compromise administrative systems, they cannot forge signatures on hardware security modules or multi-signature wallets where keys never touch networked computers.
The emergence of Mach-O Man also prompts skepticism about platform security responsibilities. Apple has invested heavily in macOS security features like Gatekeeper, XProtect, and System Integrity Protection. How effectively these mechanisms can be hardened against social engineering attacks, where users deliberately bypass protections, remains an open question. Crypto-focused security tools that integrate with hardware wallets, such as those we cover in our hardware wallet comparison guide, provide additional protection layers that don’t depend on operating system defenses alone.
What This Means for Crypto Security Going Forward
The Mach-O Man campaign represents a maturation of the threat facing crypto institutions. State-sponsored actors have moved beyond simply exploiting smart contract bugs or protocol design flaws. They’re now targeting the humans who operate these systems, recognizing that social engineering often provides an easier path than technical exploitation.
This shift demands a corresponding evolution in industry security practices. Technical audits of smart contracts remain necessary but are no longer sufficient. Organizations must also audit their operational security procedures, training programs, and communication protocols. The weakest link in a crypto organization’s security chain may not be code but people.
For individual users following these threats on our derivatives dashboard or checking trending coins, the takeaway is vigilance around all digital communications. The days when crypto security meant simply protecting seed phrases are over. Modern threats can compromise systems through mundane interactions that don’t involve private keys at all, then lie in wait for opportunities to strike.
The broader financial industry learned similar lessons over the past two decades as bank heists evolved from physical vault robberies to sophisticated cyber operations. Crypto’s accelerated timeline means absorbing those lessons in years rather than decades, while operating in a regulatory environment with fewer standardized security requirements.
Newson’s comparison to how traditional banks view nation-state threats points toward the necessary mindset shift. Banks spend billions annually on cybersecurity not because they expect to prevent all attacks but because they accept that adversaries are persistent, well-funded, and creative. Crypto institutions that survive the current threat environment will be those that internalize the same perspective.
With Lazarus Group demonstrating it can execute multiple major operations simultaneously while deploying new attack vectors, the industry’s April losses may just be the opening chapter of an intensified campaign. Organizations planning their security postures should assume the threat level will increase rather than plateau.
Related Reading
- Browse coins by sector
- What is Ethereum? Smart contracts explained
- Security news
- More on Lazarus Group
- More on macOS Malware
Sources
Final note: best-effort reporting, no guarantees on price direction, no guidance on what you should do. Treat this as context, not a roadmap.


