More than $500 million vanished from decentralized finance protocols in just over two weeks, with security researchers tracing both attacks to North Korea’s Lazarus Group. The Drift breach on social engineering and the Kelp exploit on cross-chain infrastructure signal something more coordinated than opportunistic hacking: a state-level operation treating crypto as a procurement channel.
“This is not a series of incidents; it is a cadence,” said Alexander Urbelis, chief information security officer and general counsel at ENS Labs. “You cannot patch your way out of a procurement schedule.”
That framing shifts how the industry should think about these breaches. Individual protocol teams can harden their systems, audit their code, run bug bounties. None of that addresses the underlying problem when a nation-state with sanctioned finances decides that Ethereum and its restaking derivatives are easier to loot than traditional banking rails.

The Kelp Attack Did Not Break Cryptography
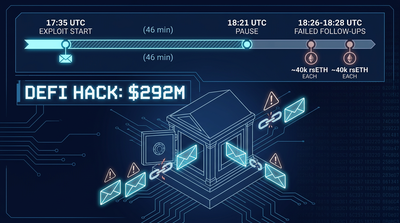
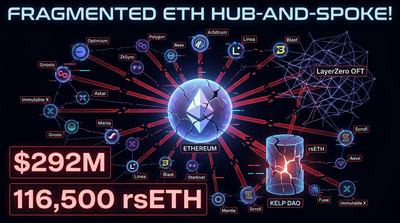
The technical details of the Kelp exploit matter because they reveal a pattern. Kelp is a restaking protocol tied into LayerZero’s cross-chain infrastructure, letting users reuse staked assets across different networks. The attack did not crack any keys. It did not find a bug in the smart contract logic. The system worked exactly as designed.
What the attackers did was manipulate the data feeding into the system, forcing Kelp’s verification layer to approve transactions that never actually occurred. Think of it like a forged shipping manifest: the signature on the document is authentic, but the contents are lies.
“The security failure is simple: a signed lie is still a lie,” Urbelis said. “Signatures guarantee authorship; they do not guarantee truth.”
David Schwed, COO of blockchain security firm SVRN, put it more directly: “This attack wasn’t about breaking cryptography. It was about exploiting how the system was set up.”
The setup in question was a configuration choice. Kelp relied on a single verifier to approve cross-chain messages. One checker. That design is faster and simpler to implement, which is why protocols adopt it. But it removes the redundancy that makes systems resilient. If your apartment building has one fire exit and someone blocks it, everyone burns.
LayerZero has since recommended using multiple independent verifiers to approve transactions, similar to requiring multiple signatures on a bank transfer. The recommendation came after the exploit, which raises an obvious question: why was the single-verifier option available at all?
Default Settings and Security Theater
Some in the ecosystem have pushed back on LayerZero’s post-exploit guidance, noting that the single-verifier setup was the default configuration. That distinction matters. Developers building on infrastructure tend to trust that defaults are sane. If you download a web framework and it ships with debug mode enabled in production, the framework bears some responsibility when someone gets hacked.
“If you’ve identified a configuration as unsafe, don’t ship it as an option,” Schwed said. “Security that depends on everyone reading the docs and getting it right is not realistic.”
This is a recurring theme in crypto security. Protocols advertise decentralization while shipping centralized defaults. Marketing materials describe trustless systems while the actual architecture includes single points of failure. The gap between promise and implementation creates attack surface.
“A single verifier is not decentralized,” Schwed said. “It’s a centralized decentralized verifier.”
Urbelis framed the problem in broader terms: “Decentralization is not a property a system has. It is a series of choices. And the stack is only as strong as its most centralized layer.”
That observation applies beyond Kelp. Every DeFi protocol sits atop layers of infrastructure: oracles, bridges, data providers, sequencers. Many of those layers have fewer participants than the protocols they support. Attackers have learned to look down the stack rather than at the visible application. Why try to crack a smart contract when you can compromise the data it trusts?
Contagion Across DeFi
The Kelp exploit did not stay contained. Like many DeFi systems, Kelp’s assets are used across multiple platforms. Restaked tokens serve as collateral elsewhere. When those tokens became compromised, the problem spread.
“These assets are a chain of IOUs,” Schwed said. “And the chain is only as strong as the controls on each link.”
Lending platforms like Aave that accepted the impacted assets as collateral are now dealing with losses. A single exploit became a wider stress event, illustrating how composability (DeFi’s superpower) doubles as systemic risk. The same interconnection that lets users move assets frictionlessly also lets exploits propagate.
This pattern has played out before. The Ethereum Activity Hits Highs, But ETH Price and Fees Keep Falling story from March documented how record smart contract activity coexisted with falling prices, partly because increased DeFi complexity introduces new failure modes that spook institutional capital.
The Kelp fallout adds another data point. Protocols that compose on top of each other inherit each other’s security assumptions. When those assumptions fail, the cascade can exceed the original breach. Risk teams at lending protocols now face a difficult question: how do you price collateral when the underlying asset’s integrity depends on infrastructure you do not control?
Lazarus Group’s Evolving Playbook
The Drift hack, which preceded Kelp by less than three weeks, used social engineering. Someone inside the trading firm was compromised, giving attackers access to internal systems. Classic spearphishing, executed at scale.
Kelp was different. No social engineering. No stolen credentials. The attackers exploited structural weaknesses in the cross-chain infrastructure itself. That evolution suggests Lazarus is not just opportunistic but adaptive, probing different attack vectors and learning from each operation.
Urbelis noted that the group has begun zeroing in on cross-chain and restaking infrastructure specifically. These layers move assets between systems and allow them to be reused, concentrating value in ways that make them attractive targets. They are also complex, often poorly understood even by developers building on top of them.
For North Korea, the math is straightforward. The regime operates under severe sanctions. Traditional finance has largely cut it off. Crypto offers a workaround: decentralized systems that do not enforce OFAC lists at the protocol level. If you can steal $500 million in two weeks, that is material revenue for a state budget.
“You cannot patch your way out of a procurement schedule.” Urbelis’s line keeps echoing because it captures the asymmetry. Protocol teams operate on development cycles. They ship updates, respond to audits, fix bugs when found. Lazarus operates on a budget cycle. They need a certain amount of funds by certain dates to finance whatever sanctioned activities require financing. That creates sustained pressure, not isolated incidents.
What Configurations Actually Protect Users
The post-Kelp recommendations from LayerZero (use multiple independent verifiers) point toward a broader principle: redundancy matters more than elegance. Systems that require multiple independent parties to agree before approving transactions are harder to compromise because attackers must subvert multiple nodes simultaneously.
This is not a novel insight. Multi-signature wallets have been standard practice for large holdings for years. Threshold cryptography spreads key material across multiple parties. The concept is well-established. The problem is that speed and simplicity compete with security, and in a fast-moving market, speed often wins.
Protocols launching into competitive markets want to minimize friction. Single-verifier setups are faster. Simpler onboarding flows attract more users. The security tradeoffs get buried in documentation that most users never read and many developers only skim.
Schwed’s critique applies: security that depends on everyone reading the docs is not realistic. If the secure configuration is opt-in rather than default, most deployments will run the insecure version. Infrastructure providers bear responsibility for what they ship, not just what they recommend in footnotes.
For users and liquidity providers interacting with DeFi, the practical lesson is uncomfortable. The protocols you use sit atop infrastructure you probably do not understand. The teams building that infrastructure may have shipped insecure defaults for speed. The assets you hold may serve as collateral elsewhere, meaning an exploit you never heard of can impair your position.
One way to think about this: would you park your car in a lot where the security guard only checks if the person handing over keys has a key, not whether they own the car? That is roughly what single-verifier cross-chain infrastructure does. It checks signatures, not truth.
The Industry’s Response Gap
After major exploits, the crypto industry typically responds with calls for better audits, more rigorous testing, improved standards. Those responses are not wrong, but they may be insufficient against state-level adversaries with sustained operational budgets.
Audits catch bugs. They do not catch adversarial manipulation of correctly functioning systems. If the code does exactly what it is supposed to do, but the inputs are lies, the audit passed and the users still lost money.
The derivatives market offers a parallel. Funding rates and liquidation mechanics work as designed even when traders get wiped out. The system is functioning. The outcomes just do not feel like success. Our derivatives dashboard tracks those mechanics across perpetual markets, but the design assumptions behind funding rate calculations are distinct from the infrastructure risks Kelp exposed.
Cross-chain security requires thinking about failure modes that audits do not traditionally cover. Who provides the data? How many independent sources confirm it? What happens if one source is compromised? These questions matter more than code elegance when attackers target the oracle layer rather than the smart contract layer.
Some projects are moving toward more robust verification setups. Others are exploring formal verification methods that prove certain properties of systems mathematically rather than testing them empirically. Neither approach is a complete solution, but both reflect growing recognition that the current state of cross-chain security is inadequate.
North Korea as Permanent Threat Actor
The Drift and Kelp exploits are not anomalies. North Korea has been hitting crypto targets for years, with Lazarus Group attributed to billions in cumulative thefts. The Bybit hack in early 2025, the Ronin bridge exploit in 2022, and dozens of smaller incidents form a pattern. The scale has grown. The sophistication has grown. The targets have shifted from centralized exchanges toward DeFi infrastructure.
That shift makes sense from the attacker’s perspective. Centralized exchanges have hardened their security significantly after years of breaches. They employ professional security teams, run red team exercises, coordinate with law enforcement. DeFi protocols, by contrast, are often built by small teams focused on shipping features. Security comes second to market fit. Infrastructure layers receive even less scrutiny.
Crypto’s permissionless nature, which enables innovation without gatekeepers, also enables exploitation without barriers. A sanctioned state actor can interact with DeFi protocols as easily as any other user. The protocols do not know or care who is on the other end. That is the point of decentralization. It is also the vulnerability.
Urbelis’s observation that “decentralization is a series of choices” implies that those choices have tradeoffs. Choosing speed over redundancy, simplicity over security, growth over governance all produce systems that work well under normal conditions and fail catastrophically under adversarial pressure. Lazarus applies adversarial pressure professionally.
Where This Leaves the Ecosystem
The $500 million lost across Drift and Kelp in two weeks will not be recovered. Funds traceable to Lazarus typically move through mixing services and eventually into state coffers. The losses fall on the protocols, their users, and anyone holding collateral that depended on the integrity of the breached systems.
For protocol teams, the lesson is architectural. Single points of failure, regardless of how convenient, are targets. Defaults matter more than documentation. Composability spreads risk as effectively as it spreads utility. None of these insights are new, but the Kelp exploit makes them expensive to ignore.
For users, the lesson is epistemic. You do not understand the full stack beneath the protocols you use. Neither do most of the developers building on top of it. Certainty about security is unfounded. Sizing positions to survive undiscovered risks is more realistic than believing audits prevent all exploits.
For the industry collectively, the lesson may be political. State-level adversaries operating on procurement schedules require responses beyond code patches and configuration changes. Whether that means better coordination with law enforcement, industry-wide security standards with enforcement mechanisms, or acceptance that some attack surface is permanent, the current equilibrium is clearly unstable.
Lazarus will keep probing. The next target may be another restaking protocol, or a bridge, or an oracle network, or something further down the stack that nobody has audited carefully. The cadence continues regardless of what any individual protocol does. Crypto built permissionless systems. North Korea uses them.
Related Reading
Sources
Nothing in this article constitutes investment advice. Cryptocurrency carries risk, always do your own due diligence.