“Things can happen when you trust one single party, whoever that would be.”
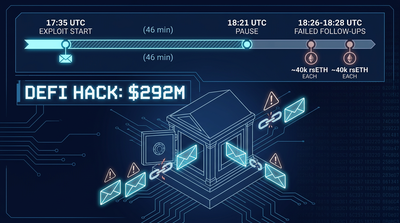
That observation from Curve Finance founder Michael Egorov cuts to the heart of what went wrong over the weekend, when a roughly $292 million exploit of Kelp DAO sent shockwaves through decentralized finance. The attack did not require sophisticated zero-day exploits or novel cryptographic breaks. It exploited something far simpler: a bridge component that trusted a single signer to verify transactions. Once that signer was compromised (or fooled, or misconfigured, the investigation is still ongoing), the rest unfolded with grim predictability.
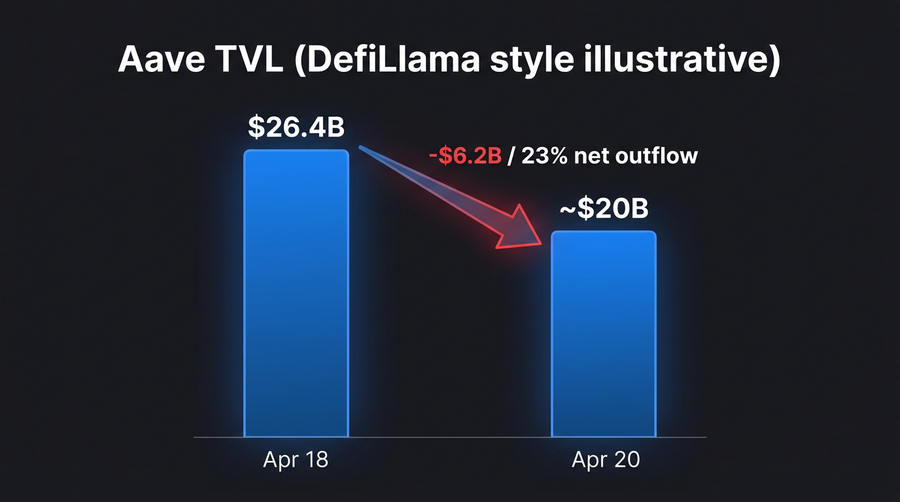
The fallout has been severe. Aave, the largest decentralized lending protocol in crypto, is now sitting on collateral that may be worthless, and users have pulled approximately $6 billion from the platform in what some observers are calling a bank run. Ledger’s CTO Charles Guillemet told CoinDesk that 2026 will “most likely be the worst year in hacks,” with trust in DeFi having “eroded” further after this latest incident.
The Anatomy of a Bridge Exploit
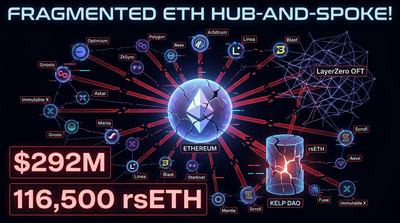
Bridges are the plumbing of multi-chain DeFi. They allow assets to move from one blockchain to another by locking tokens on the source chain and minting equivalent representations on the destination. The security of this system depends entirely on whoever confirms that the original deposit actually happened. In Kelp’s case, that verifier was a 1-of-1 signer setup, meaning a single entity could approve any transaction without additional checks.
According to Guillemet, the attacker managed to sign a message that allowed them to mint large amounts of rsETH, Kelp’s yield-bearing Ethereum derivative, on the destination chain. No corresponding assets were ever locked on the source side. The tokens were created from nothing.
“It seems the attacker was able to sign a message allowing him to mint large amount of rsETH,” Guillemet explained, adding that how that signing access was obtained remains unclear. The system relied on LayerZero’s official node infrastructure, raising uncomfortable questions about whether the node itself was hacked, tricked by malformed data, or simply misconfigured.
“Was it hacked? Was it fooled? We don’t know,” Egorov said.
What happened next was textbook DeFi arbitrage, just executed by a thief. The freshly minted rsETH, now existing on the destination chain with no real backing, was immediately deposited into lending protocols. Aave took the brunt of it. The attacker borrowed real ETH against the phantom collateral, then vanished with the proceeds.
The attack shares structural similarities with the Drift protocol exploit from just two weeks earlier, which drained $285 million from Solana-based markets. Both incidents exploited points where human trust intersects with automated systems. Both left lending protocols holding bags of questionable collateral.
Why Aave’s Problem Is Everyone’s Problem
The immediate damage to Kelp DAO is obvious: they lost control of their bridge and their token’s integrity is now in question. But the downstream effects may prove more consequential for the broader DeFi ecosystem.
Aave is now holding rsETH that cannot realistically be liquidated. The token’s value depends on Kelp’s ability to honor redemptions, which is compromised given that the backing assets were never deposited. Meanwhile, the ETH borrowed against that collateral is gone. The protocol faces what Egorov described bluntly: “Aave was left with rsETH which cannot be really sold and maxborrowed ETH, so no one can withdraw ETH.”
That dynamic created the conditions for a classic bank run. When word spread that Aave might be sitting on hundreds of millions in bad debt, users rushed to withdraw whatever assets they could. The protocol saw approximately $6 billion in outflows following the incident, a staggering sum that represents a significant fraction of its total deposits. The AAVE token dropped about 15% in the 24 hours following the attack.
For readers tracking DeFi sector movements, this is the second major lending market crisis in a month. The interconnected nature of these protocols means that stress in one market can propagate quickly. When Aave’s ETH liquidity dried up, users who needed to withdraw for other positions elsewhere found themselves stuck, creating ripple effects across the ecosystem.
| Protocol | Status After Exploit | Estimated Exposure |
|---|---|---|
| Aave | Holding illiquid rsETH collateral | Hundreds of millions (unconfirmed) |
| Kelp DAO | Bridge compromised, rsETH backing questioned | $292M direct loss |
| Other lenders | Exposure under investigation | TBD |
Egorov pointed to a structural issue that amplified the damage: non-isolated lending models where assets share risk across pools. In such systems, one bad asset can poison the entire pool’s risk profile. He argued that Kelp’s 1-of-1 verifier configuration should have been flagged during onboarding to lending platforms like Aave. “Configurations like this should have been flagged earlier,” he said.
2026: DeFi’s Year of Living Dangerously
The timing could not be worse for an industry trying to rebuild credibility with institutional investors. The total value locked in DeFi protocols stands at nearly $90 billion, a figure that looks increasingly precarious given the frequency and scale of exploits this year.
Guillemet did not mince words about the trajectory: 2026 is “shaping up to be DeFi’s worst year in terms of hacks.” Coming just weeks after the Drift incident, the Kelp exploit reinforces a pattern. Bridges, in particular, have become the industry’s most dangerous attack surface. They concentrate enormous value, depend on complex multi-chain logic, and often rely on trust assumptions that look reasonable in a whitepaper but prove fragile under adversarial pressure.
The investigation into how exactly the signer was compromised continues. Guillemet noted that the attacker demonstrated clear sophistication, suggesting this was not the work of opportunistic amateurs. Whether that points toward a state actor, an organized criminal operation, or an inside job remains speculation at this stage.
Egorov, for his part, offered a glass-half-full interpretation of the carnage. “Crypto is a harsh environment which no bank would have survived, yet we are working with that,” he said. “I think DeFi will learn from this incident and become stronger than before.”
That optimism may prove warranted over the long term. Previous exploits have led to genuine improvements in bridge design, oracle redundancy, and collateral risk modeling. But for users who woke up Sunday morning to find their lending deposits trapped or devalued, the learning process feels distinctly one-sided.
For those monitoring the fallout, our derivatives dashboard shows elevated liquidation activity across ETH perpetuals as traders adjust to the changed risk landscape. The fear gauge has predictably spiked, tracking at extreme fear territory according to the Fear & Greed Index.
The deeper question the exploit raises is whether DeFi’s composability, often touted as its greatest strength, has become an unmanageable liability. When protocols are deeply interconnected, the failure of one component does not stay contained. It cascades. A bridge exploit becomes a lending crisis becomes a liquidity crunch becomes a bank run. Each step follows logically from the last.
Until the industry develops better circuit breakers, better pre-listing due diligence for collateral assets, and more redundant trust assumptions for cross-chain operations, these cascades will keep happening. The scale may vary. The mechanics will differ. But the pattern, one weak link dragging down the chain, will persist.
Whether users’ appetite for DeFi yields will survive another year like this one is the open question no one can confidently answer.
Related Reading
- DeFi yield farming: the beginner’s walkthrough
- DeFi news
- More on Kelp DAO
- More on Aave
- More on LayerZero
Sources
This content is educational, not financial advice. Digital asset investments can lose value. Research thoroughly before investing.