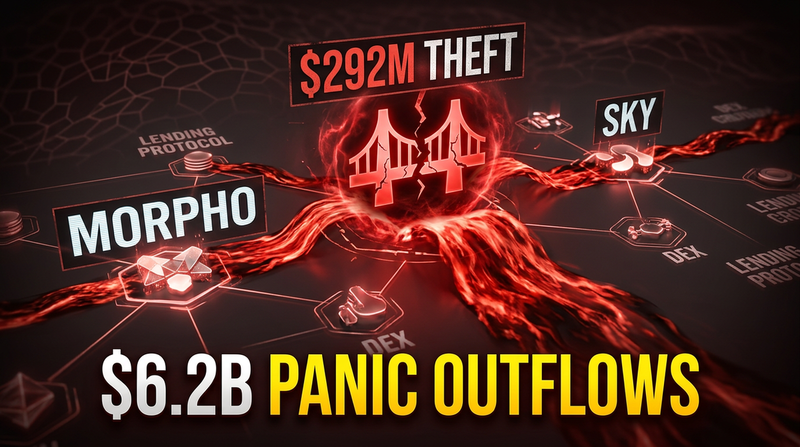
Panic hit Ethereum lending markets over the weekend as the fallout from the Kelp DAO bridge exploit cascaded through the entire DeFi ecosystem. What started as a $292 million theft turned into something far more unsettling: a full-scale bank run on Aave, the largest decentralized lending protocol, and a crisis of confidence that has traders openly questioning whether the current architecture of DeFi can survive its own complexity.
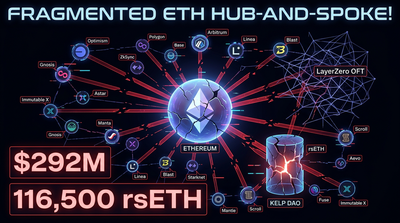
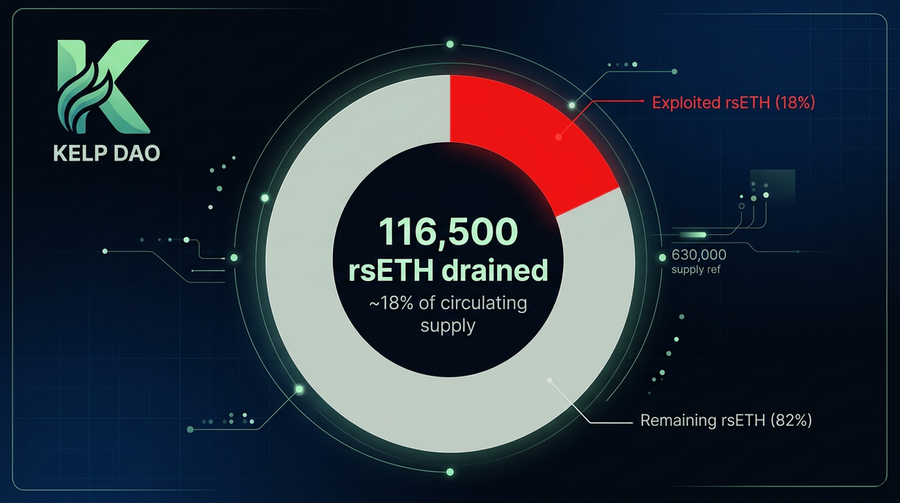
The attack drained roughly 116,500 rsETH tokens from Kelp DAO’s cross-chain bridge, representing about 18% of the total rsETH supply. Within hours, depositors across multiple lending platforms, including some with zero direct exposure to the stolen asset, began yanking their funds. The industry had seen hacks before, plenty of them, but this one felt different. The speed of contagion suggested structural vulnerabilities that protocols had either ignored or failed to anticipate.
Aave Bleeds $6 Billion as Depositors Flee
Aave’s total value locked collapsed from $26.4 billion on April 18 to roughly $20 billion by Sunday morning U.S. time, according to DefiLlama data. That represents a net outflow of approximately $6.2 billion, or 23%, in less than 48 hours. The AAVE token dropped more than 18% as the weekend selling intensified.
Stani Kulechov, Aave’s founder, was quick to clarify that the protocol’s smart contracts were not compromised. The exploit happened at Kelp DAO, not within Aave itself. But that distinction didn’t matter much to depositors watching rsETH lose its peg and wondering which domino would fall next.
The dynamics inside the lending markets turned ugly fast. One market observer, Josu San Martin, described what was happening in Aave’s ETH markets: depositors who wanted out but couldn’t withdraw their underlying Ethereum were borrowing stablecoins against their collateral just to extract liquidity. That’s not a withdrawal in the traditional sense. It’s a workaround, and it creates its own feedback loop of stress. “This is a full on run on AAVE,” San Martin wrote.
As we reported when the breach first emerged, emergency freezes hit markets across Aave, SparkLend, and multiple other protocols as risk teams scrambled to contain exposure. The problem is that once users see freezes happening somewhere, they start pre-emptively withdrawing from everywhere.
Data shared by 0xngmi showed the spillover wasn’t limited to Ethereum. “The rsETH hack is leading to withdrawals across all lending protocols, even on Solana and unaffected protocols,” the post noted, citing declines at Morpho, Sky, and JupLend. The contagion had jumped chains.
The Verification Layer Was the Weak Link
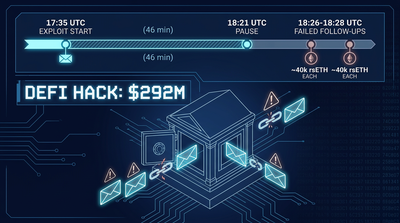
Engineers spent the weekend dissecting what went wrong at the technical level, and the picture that emerged was both straightforward and alarming.
The exploit didn’t involve breaking smart contract code in the traditional sense. The contracts worked exactly as designed. The problem was that the design itself, specifically how Kelp DAO configured its cross-chain verification, left a gaping hole.
That quote, from a technical breakdown by a developer going by cryptogoblin, captures the mechanism. The attacker managed to convince LayerZero’s cross-chain messaging layer that a valid instruction had arrived from another network. Kelp’s bridge accepted that instruction and released the tokens to an address the attacker controlled.
Cryptogoblin emphasized that this was not a LayerZero protocol bug but a configuration issue. Every project using cross-chain tokens, the developer argued, should be studying this incident today.
But not everyone was willing to let LayerZero’s architecture off the hook. A critic posting as Fishy Catfish framed the incident as a design flaw at a more fundamental level. The argument centers on something called DVNs, or Decentralized Verifier Networks. In LayerZero’s V2 system, DVNs are independent entities that validate messages between blockchains. They check that a message hash on the source chain matches what’s expected on the destination chain.
The problem, according to this critique, is that there’s no security floor. A protocol can configure its verification as a single DVN run by a single entity. That’s permitted under the current design. “Imagine if a roller coaster manufacturer allowed amusement parks to individually decide what the minimum safety specs were,” the post read.
The analogy lands. Flexibility is supposed to be a feature of modular blockchain infrastructure. Protocols can customize their security setups based on their needs and resources. But flexibility without guardrails means that some setups will inevitably be weak, and users interacting with those protocols may have no easy way to evaluate the risk they’re taking.
Why Modular Security Became a Systemic Risk
The debate over modular security has been simmering in DeFi circles for years, but the Kelp DAO exploit may force a reckoning.
The pitch for modular security is intuitive. Instead of forcing every protocol to use the same verification mechanism, you let them mix and match. Some might want maximum decentralization and pay for multiple independent verifiers. Others might prioritize speed and cost, accepting a leaner setup. In theory, this creates a market for security where projects can find their own equilibrium.
In practice, the cheapest option tends to win. Protocols facing competitive pressure to keep fees low and throughput high will often select minimal verification, especially if their users aren’t sophisticated enough to notice or care. The result is a landscape where some bridges are far more vulnerable than others, but they all look similar from the outside.
Fishy Catfish argued that modular security remains a worthwhile design space, but only if the range of options has a native security floor that is quite strong. Additional security layers could be added on top for high-value use cases. Without that baseline, you get what happened this weekend: a single misconfigured verification point enabling a nine-figure theft.
The Kelp DAO incident also highlights how interconnected DeFi has become. RsETH wasn’t just sitting in one place. Liquid restaking tokens are designed to be used as collateral across multiple platforms, deployed in yield strategies, and moved between chains. When 18% of the supply gets compromised, the ripple effects touch everything that token touched.
Our earlier coverage of the breach’s aftermath detailed how rsETH became stranded across 20 different chains as markets froze. Layer 2 holders were left wondering whether their balances were even real. That kind of uncertainty doesn’t stay contained.
A Pattern Emerges in 2026’s Hack Wave
Kelp DAO wasn’t an isolated incident. It’s the largest DeFi exploit of 2026 so far, but it follows a string of significant hacks this month alone. The pattern has intensified doubts about whether the sector can deliver on its promises of permissionless, self-custodied finance.
The phrase “DeFi is dead” started circulating on crypto social media over the weekend, part gallows humor and part genuine frustration. Nobody thinks decentralized protocols are literally going to disappear. But the sentiment reflects exhaustion with a system that seems to produce regular multi-hundred-million-dollar disasters.
Protocols responded to the Kelp incident by freezing affected markets and launching urgent reviews of their own cross-chain configurations. That’s the right immediate response. But it also underscores how reactive the industry remains. There’s no central authority to mandate security standards, and the governance structures that do exist move slowly. By the time a protocol updates its verification setup, the next exploit may have already happened somewhere else.
The market mechanics of this weekend’s panic also revealed how thin liquidity can become during stress events. When everyone tries to exit at once, the machinery breaks down. Depositors borrowing stablecoins because they can’t withdraw ETH is a sign that the system wasn’t designed for bank runs. Neither was traditional finance, of course. Banks rely on deposit insurance and central bank backstops. DeFi explicitly rejects those mechanisms. The question is whether it has found adequate substitutes.
For anyone tracking the DeFi sector more broadly, the Kelp DAO incident is a stress test that the ecosystem failed. TVL across major protocols dropped sharply, not because of widespread contract failures but because of fear. Fear that the next protocol might be misconfigured. Fear that the token you’re holding might have invisible counterparty risk. Fear that the complexity everyone celebrated as innovation has become a liability.
Can Cross-Chain Infrastructure Be Fixed?
The technical postmortems are still being written, but some themes are already clear.
LayerZero and similar cross-chain messaging protocols will face pressure to implement stronger default security settings. Whether they do so voluntarily or under threat of user exodus remains to be seen. The competitive dynamics in bridging infrastructure are brutal. Any protocol that slows down or becomes more expensive risks losing market share to a faster, cheaper alternative, even if the cheaper alternative is less secure.
Protocols that depend on bridged assets will need to reconsider how they evaluate risk. Listing a liquid restaking token or accepting it as collateral isn’t just a question of the token’s on-chain mechanics. It’s a question of the entire bridge infrastructure that token depends on. That assessment is hard. Most teams don’t have the resources to audit every piece of third-party code their protocol touches.
Users, meanwhile, are left to make their own judgments with incomplete information. The DeFi ethos has always emphasized self-sovereignty. You control your keys, you verify the code, you accept the risk. In reality, almost nobody reads smart contracts before depositing funds. And even sophisticated users can’t evaluate the security configuration of every bridge their assets might cross.
The Aave bank run showed what happens when that implicit trust breaks down. Kulechov could say the protocol wasn’t compromised, and he was right. But users withdrew anyway, because the incident reminded them that DeFi is a system of systems, and weakness anywhere can become a problem everywhere.
Some observers have argued that the industry needs minimum security standards enforced at the protocol level, essentially a building code for DeFi. Others counter that such standards would undermine the permissionless ethos that makes decentralized finance attractive in the first place. Who gets to decide what’s secure enough? And what happens to protocols that don’t comply?
Those questions don’t have clean answers. What’s certain is that this weekend’s events will influence how capital allocates across DeFi in the months ahead. Protocols with clear, audited, robust security setups may attract a premium. Those with opaque or flexible configurations may face harder questions from depositors and integrators alike.
The $292 million is gone. The larger damage, the erosion of confidence in an ecosystem that was supposed to be the future of finance, is harder to quantify but may prove more durable. Whether DeFi can rebuild that confidence depends on whether this weekend’s panic leads to structural changes or just fades into the long list of hacks that the industry has learned to shrug off.
Related Reading
Sources
This content is educational, not financial advice. Digital asset investments can lose value. Research thoroughly before investing.