Quantum computing has moved from distant theoretical threat to active discussion in Bitcoin’s core development community over the past two years. A 2026 warning from a Nobel-laureate physicist that a sufficiently powerful quantum computer could break Bitcoin’s signature scheme in about 9 minutes moved the conversation from academic circles to mainstream crypto media. The timeline for “sufficiently powerful” remains the central uncertainty, but the community has started seriously working on migration paths where previously it had mostly deferred the question.
This guide covers what’s actually at risk, how urgent the threat is, and what Bitcoin’s upgrade options look like. It’s written for retail holders who want to understand the situation without either dismissing it or panicking.
What quantum computers actually do to Bitcoin
Bitcoin’s security relies on two cryptographic primitives. Hash functions (SHA-256 and RIPEMD-160) are used to create Bitcoin addresses from public keys. Elliptic curve digital signatures (ECDSA on the secp256k1 curve) are used to sign transactions, proving you own the private key for an address.
Hash functions are considered quantum-resistant in practice. Grover’s algorithm provides a quadratic speedup for brute-forcing hashes, but effectively doubles the required hash length to maintain security, and Bitcoin’s 256-bit hashes remain secure against this attack at any reasonable quantum-computer scale.
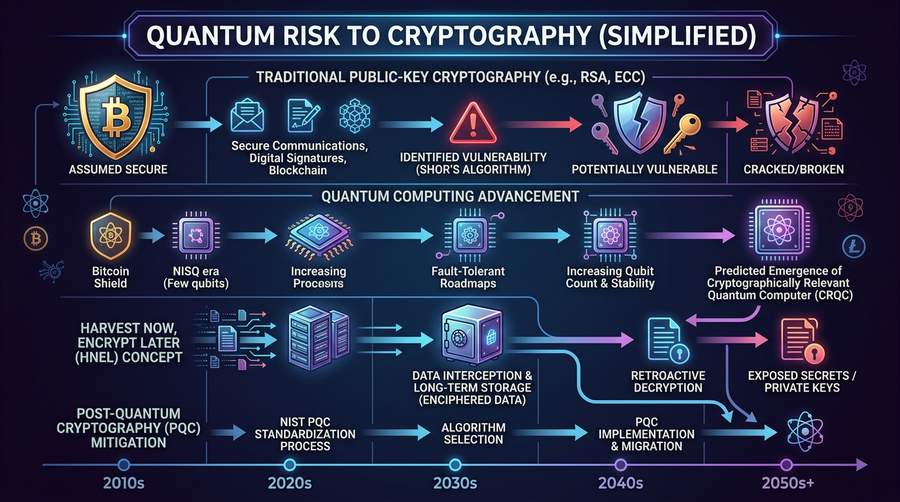
Elliptic curve signatures are the vulnerable part. Shor’s algorithm, when run on a sufficiently large quantum computer, can recover a private key from its corresponding public key in polynomial time. This breaks ECDSA entirely. A quantum computer with the right scale running Shor could take any known Bitcoin public key and derive the private key that signs transactions for it.
The critical distinction: Bitcoin addresses aren’t public keys. They’re hashes of public keys. The address is quantum-safe; the underlying public key is not. A public key only becomes visible on the blockchain when the address makes an outgoing transaction — the transaction reveals the public key to validate the signature.
The 6.9M BTC at risk
Bitcoin in addresses that have never spent coins (receive-only addresses) is protected behind the hash layer. A quantum computer cannot derive the private key from the address alone.
Bitcoin in addresses whose public key has been revealed is vulnerable once a sufficient quantum computer exists. This includes:
- P2PK (Pay-to-Public-Key) addresses used in the earliest Bitcoin days, before Satoshi designed the P2PKH pattern. These use raw public keys directly; ~1.5M BTC is estimated to sit in P2PK addresses, much of it in early blocks often attributed to Satoshi.
- Any address that has made an outgoing transaction. Spending from an address reveals the public key in the transaction data.
- Any address that has been reused. Reuse of the same address for receiving multiple times is considered poor practice for privacy reasons; from a quantum-security view, reuse also means the public key is exposed from the first spend onward.
Research estimates put the total exposed BTC at roughly 6.9M, or about 33% of all Bitcoin in circulation. The exact number depends on how you count reused-but-otherwise-secure addresses and a few edge cases.
For a retail holder, the practical implication: any BTC sent to a fresh address and never moved stays quantum-safe. BTC that’s been spent from (especially repeatedly) has its public key published on the blockchain and is vulnerable when quantum computers reach attack scale.
The timeline question
Headlines suggest imminent risk. Academic estimates suggest longer timelines. Both can be right because they measure different things.
The 9-minute attack from the 2026 Nobel-laureate estimate assumed a quantum computer with millions of logical qubits, sufficient fidelity, and enough quantum volume to run Shor’s algorithm at Bitcoin-public-key scale. That machine does not exist and is not close to existing.
Today’s quantum computers have around 1,000-2,000 physical qubits in their largest variants. After quantum error correction (which costs dramatic overhead in physical qubits per logical qubit), usable logical qubits are in the tens to low hundreds. Shor’s algorithm against 256-bit ECDSA requires thousands of logical qubits with low error rates over long computation times. Current hardware is not close to this threshold.
Credible academic timelines for cryptographically-relevant quantum computers range from 10 to 30 years out. The range reflects uncertainty about which quantum computing approaches (superconducting, trapped ion, photonic, neutral atom, topological) advance fastest. Faster-than-expected progress in any of these modalities could compress the timeline; slower-than-expected progress extends it.
A reasonable planning assumption for Bitcoin: the network probably has 10+ years before a practical quantum attack is feasible, and could have 20-30. Complacency is wrong; imminent panic is also wrong. Migration infrastructure needs to ship well before the attack becomes possible, which means it needs to be in serious development now.
Bitcoin’s upgrade options
Bitcoin has several potential paths to quantum resistance.
BIP360 proposes adding post-quantum signature schemes alongside existing ECDSA. The primary candidate is the Dilithium signature scheme, a lattice-based algorithm that’s been standardized by NIST as part of the post-quantum cryptography effort. Alternative proposals use SPHINCS+ (hash-based signatures) or other schemes. BIP360 would roll out as a soft fork adding new address types; users migrate by sending coins to the new address types over time.
Contested design questions:
- Freeze vs migrate. Should vulnerable coins that haven’t migrated by a deadline be frozen (made unspendable) to prevent quantum theft? A freeze is technically possible via a soft fork but has obvious political problems — lost coins belong to real people, freezing them is a form of dispossession. The alternative is accepting that quantum computers will drain vulnerable coins to the attacker, which is also bad.
- Signature size. Post-quantum signatures are much larger than ECDSA (Dilithium signatures are ~2.5KB vs ECDSA’s ~71 bytes). This changes Bitcoin’s block capacity and transaction cost economics significantly.
- Hybrid schemes. Running both ECDSA and post-quantum signatures for a migration period protects against the risk that the chosen post-quantum scheme turns out to have a flaw. Adds complexity.
Adam Back (Blockstream CEO) has publicly advocated for an “optional upgrade” approach where users can migrate to quantum-resistant addresses when they choose, without forcing a hard cutoff. Other developers argue this leaves too much exposed BTC for too long.
The discussion in 2025-2026 has been more active than in any prior period. A consensus solution has not emerged.
What Bitcoin holders should do
Don’t panic. The timeline is long enough that migration tools will almost certainly ship before the attack is feasible. Selling Bitcoin today over quantum concerns is bad math on the probabilities.
Don’t ignore it either. Specific actions that reduce your exposure at nearly zero cost:
- Send Bitcoin to fresh P2WPKH or P2TR addresses. Both are post-Segwit Bitcoin address types that use the hash layer, protecting the public key. Taproot addresses (P2TR) are the most recent standard and should be your default for new storage.
- Don’t reuse addresses. Each deposit to a new address. Most modern wallets do this automatically; check your wallet’s settings to confirm.
- Avoid keeping Bitcoin in P2PK or legacy P2PKH addresses. If your holdings are in older addresses, consider migrating them to P2WPKH or P2TR while you can do so safely.
- Follow BIP360 development. When migration tools become available, use them. This might be 2-5 years from a major Bitcoin Core release; might be later.
For the 6.9M BTC in vulnerable addresses, the individual holders make migration decisions individually. Satoshi’s coins (estimated ~1M BTC in P2PK addresses) are presumably unmovable. Other long-lost keys remain unreachable. For coins still controlled by their owners, migration is a choice those owners will need to make.
What this means for price and narrative
The quantum threat has become a legitimate topic for Bitcoin price analysis. Some analysts argue it justifies a risk discount to BTC until migration is complete. Others argue it’s unlikely to materialize within useful investment horizons and should be priced near zero.
A few observations:
- The Ethereum community faces the same problem. Ethereum’s signatures are also quantum-vulnerable. Any “Bitcoin quantum risk” applies to most of crypto.
- Post-quantum signature schemes exist and are being standardized. NIST’s PQC standardization has produced real algorithms that work. This is not a hypothetical countermeasure.
- Migration will happen. The economic incentive for Bitcoin (and every other cryptocurrency) to migrate before quantum computers arrive is massive. The only question is execution timeline.
For a Bitcoin holder in 2026, the sensible stance is: take address hygiene seriously, follow the technical discussion, and don’t make drastic portfolio moves based on timeline speculation.
Related reading
- What is Bitcoin? Beginner’s guide.
- Bitcoin coin page for live price and market data.
- How to buy Bitcoin.
- Bitcoin news on the Bitcoin category for ongoing quantum and security coverage.
Sources
- NIST Post-Quantum Cryptography standards
- BIP360 draft (GitHub)
- Deloitte 2020 study on Bitcoin quantum exposure
- Ethereum Foundation quantum research discussions (ethresear.ch)
Educational content, not financial advice. The quantum computing timeline is uncertain; this guide reflects credible current estimates and the state of the migration debate as of April 2026.


